9/23/2018 UPDATE: Latest PowerPoint & Handout w/ Matrix including the recommendation to use Circle with compatible NETGEAR routers.
Part 1 is a “technology parenting” overview. Part 2 is the technical “horsepower” and resource for securing your home internet connection. Securing your router is a foundation of Part 1 and, in my professional opinion, a best practice for anyone using the internet.
I am passionate about my faith, my family, and Technology. This post combines all three. Even if you do not believe in Jesus as Christ, hopefully the concepts and technical information apply to all parents.
Backstory
Over the past five years, I consulted and built a close relationship with a high-profile, local bank executive. He shared with me the struggle of raising two teenagers and the challenge Technology has been specifically for his son. Porn, inappropriate apps, excessive video games, etc. We reviewed options, put a technical and practical plan in place, and I got to see secondhand how knowledge today’s teens’ are with technology. His son promptly attempted, unsuccessfully, an iPhone restore and hard reset his Xbox 360. You get the idea.
After having individually consulted over 100 families, it is clear: parents are completely over-matched for today’s Technology with their kids. Parents with good intentions need better tools and a boost in knowledge. To test my message, I presented this material and conducted a follow-up technical workshop at our church, Calvary Church, with the counseling pastor. It confirmed the need: over 80 parents and 40 routers were issued to protect families. Here is the material.
Overview PowerPoint
First and foremost, as a parent, the focus must be on their hearts, minds, and your relationship with them. The technical aspects are to provide “guardrails” and support parenting. Please browse the PowerPoint.

Parent Technology Matrix
A visual to effective “technology parenting” is matrix that guides parents at each age on how to interact with technology. As mentioned, this is based on Christian values, but I believe it applies to all families looking to be proactive and deliberate on implementing technology in the home. Again, this matrix is a guide; browse the pdf.

Feedback
I got a wealth of feedback; mostly positive. Some parents shared this matrix is not realistic. They shared their second grader was using required iPads at school, etc. The irony is how the Children’s Online Privacy Protection Act is to protect kids under the age of 13 years old, yet kids under the age of 13 years old are the primary offenders. Parents also shared that having multiple kids, especially those that are spread out, create technical challenges on how to implement content filtering. See Part 2.
Next Steps
The technical-router-workshop is the next step and post. It goes into extensively detail on how to secure and insulate your home/business network from porn and malware. Open to your feedback; comment below.





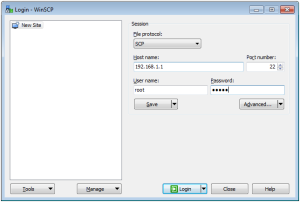





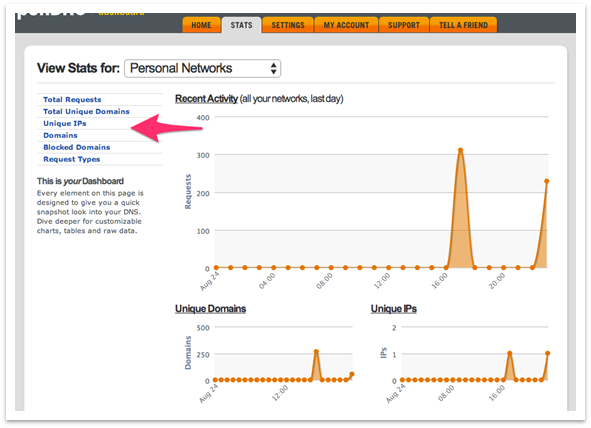
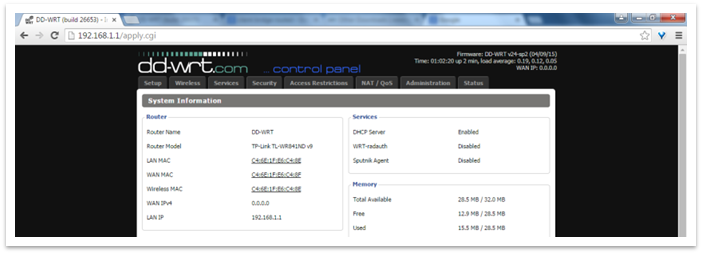 Click “Setup” at the top and enter the following when the webpage prompts you:Username: “root” / Password: “admin” (admin is the default DD-WRT password)
Click “Setup” at the top and enter the following when the webpage prompts you:Username: “root” / Password: “admin” (admin is the default DD-WRT password)




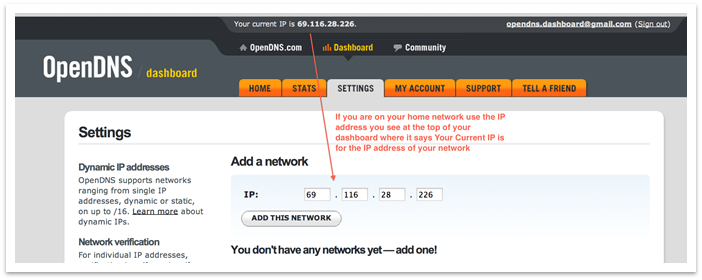
 Do not download the software under #3. The DD-WRT software on the router will handle the auto updating for you if you followed the router setup instructions above under “DDNS”. If you have more questions regarding dynamic IP addresses please see
Do not download the software under #3. The DD-WRT software on the router will handle the auto updating for you if you followed the router setup instructions above under “DDNS”. If you have more questions regarding dynamic IP addresses please see