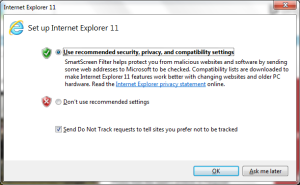
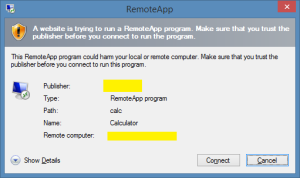
The goal was to remove this dreaded end-user dialogue box:
Simple right? Wrong; especially when I came across many blogs attempting to address RDS certificate issues. This one post gets you 90% there but was not complete. Specifically, see the red section below.
Steps:
- Get a certificate (in my case, a GoDaddy wildcard cert)
- Assign the certificate to the RDS roles. Refer to this great post with screen shots.
- Extract the certificate thumbprint, remove the “Get-Childitem Cert:\LocalMachine\My” PowerShell command on your RDS server or follow the steps outlined on Morgan Simonsen’s blog. Make sure you properly format the thumbprint: no spaces, all caps.
- Create and assign a GPO for the following settings:
- Computer Configuration > Policies > Administrative Templates > Windows Components > Remote Desktop Services > Remote Desktop Connection Client > “Specify SHA1 thumbprints of certificates representing trusted .rdp publishers”.
Under Options, paste the formatted thumbprint.

- Computer Configuration > Policies > Administrative Templates > Windows Components > Remote Desktop Services > Remote Desktop Connection Client > “Allow .rdp files from valid publishers and user’s default .rdp settings”.
Enable. - Computer Configuration > Policies > Administrative Templates > System > Credentials Delegation > “Allow Delegating Default Credentials > “Allow Delegating Default Credentials”.
Enable and add “TERMSRV/<insert your RDS gateway/server name>” (refer to the example text in the GPO editor).

- Yet after repeated gpupdate /force and a full reset of IE settings, the dialogue warning persisted. Then I stumbled across these two nuggets: here combined with 2nd post down here. The “Specify SHA1…” GPO was not adding the proper “PublisherBypassList” keys.
The solution? Manually adding the “HKEY_CURRENT_USER\Software\Microsoft\Terminal Server Client\PublisherBypassList” as a User Configuration GPO registry update.

Notice the key is the thumbprint above with an additional “00” placed at the end.
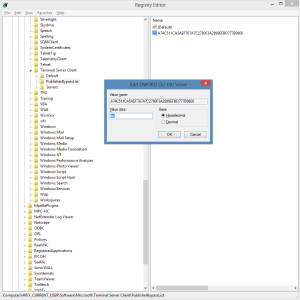
The easiest way to verify the key is to check the “Do not remind me….” on the RDS prompt. It will save the thumbprint for you in the proper format.
- Computer Configuration > Policies > Administrative Templates > Windows Components > Remote Desktop Services > Remote Desktop Connection Client > “Specify SHA1 thumbprints of certificates representing trusted .rdp publishers”.
- For icing on the cake, enable single sign-on; see this excellent blog post or the official MSDN blog post“.
Enjoy. SSO RDS connections with no dialogue boxes or end-user warnings or prompts.